The Ultimate Guide: How to Stay Safe in Crypto
In this guide, we’ll outline specific steps that you can take to stay safe in crypto.

With great power comes great responsibility. In crypto, you can be a true owner of your assets and investments. But with self-custody, only you control your assets. No authority or power can return your crypto or reverse transactions. It’s up to you to protect yourself and your funds. In this guide, we’ll outline specific steps that you can take to keep crypto safe.
Content:
- Know your enemy
- Choose the right crypto wallet
- Use separate addresses
- Secure your seed phrase and private keys
- Know and avoid common scams
- Detect phishing
- Understand your transactions
- Understand smart contract risks
- Know where to get help if you need it
1. Know your enemy
First, you need to understand who you’re up against.
Crypto criminals are in it strictly for the money. Like any business, they profit if their revenue is larger than costs.
Hackers will go after the biggest targets: exchanges, protocols, influencers, and whales. These attacks can be complicated, multi-step operations. But they will only target you (the user) personally if you are an influencer, a whale, or work for an exchange or protocol.
Alternatively, attackers might cast the net as widely as possible, aiming for lots of small targets. Attacks of this type would be automated or deployed at scale. Nobody will try to hack your wallet. They won’t even know its address. But they will try to trick you into taking an action that they want.
In this case, your own emotions are the biggest threat — scammers will try to use your greed and fear.
If you choose the right non-custodial wallet and simply store crypto, your assets will be safe in most cases.
2. Choose the right crypto wallet
You always make a tradeoff between security and convenience.
An offline, off-grid nuclear bunker with a seed phrase on titanium plates could be the safest way to store your crypto. But then you can’t do much with it.
On the other spectrum are hot crypto wallets on your phone. Mobile wallets are the most convenient way to use crypto: you can sign any transaction on the go, trade, send, mint, and more. Its software isn’t the biggest risk. Instead, the convenience means you’ll make more transactions, some of which could lead to scams.
And there are lots of options in between, each with advantages and disadvantages:
- Custodial wallet — any exchange wallet offers convenient conversion to and from fiat, but not your keys, not your coin. An exchange or another custodian can freeze your account or block withdrawals. Exchanges can also get hacked like the infamous Mt Gox or go bankrupt like FTX.
- Cold wallet — hardware wallets like Ledger securely store your private keys on a separate device, but you need to have it with you to make any transaction.
- Multisig wallet — smart contract wallets like Safe require signatures by several keys to make transactions. This requirement increases safety but demands extra time for signing messages if you have keys on several devices.
So, which crypto wallet is the best?
The best wallet depends on what you do with crypto.
However, it’s clear that to be an active Web3 citizen and stay safe, you need crypto wallets that are:
- Self-custodial — only you control your private keys;
- Audited — reputable security auditors regularly check the code;
- Open source — the core code is available for anyone to explore, increasing the likelihood that any vulnerability will be reported.
Still, don’t keep all eggs in one basket. Use several addresses, each for its purpose.
3. Use separate addresses
It’s not wise to connect an address with all your life savings to a random dapp you see on Twitter.
Instead, use several addresses for different purposes:
- Storing crypto and NFTs long-term — ideally, on cold wallets (aka hardware wallets) or an address you don’t regularly use online.
- Using DeFi — a desktop wallet, potentially a cold wallet, and multisig. You’ll make transactions to manage your portfolio, but probably once a month or once a week, not several times a day.
- Using Web3 social — an address with your ENS, Lens, and other handles to be used on both mobile and desktop wallets. You can hold there your BAYC or other fancy NFT but it’s like walking with a Rolex in a dangerous neighborhood at night.
- Minting NFTs, aping into meme tokens, yield farming — this can be a mobile wallet with the amount you are ok to see going to zero. If you hope to resell some of the newly minted NFTs, it's best to move them to another address that is used for storage.
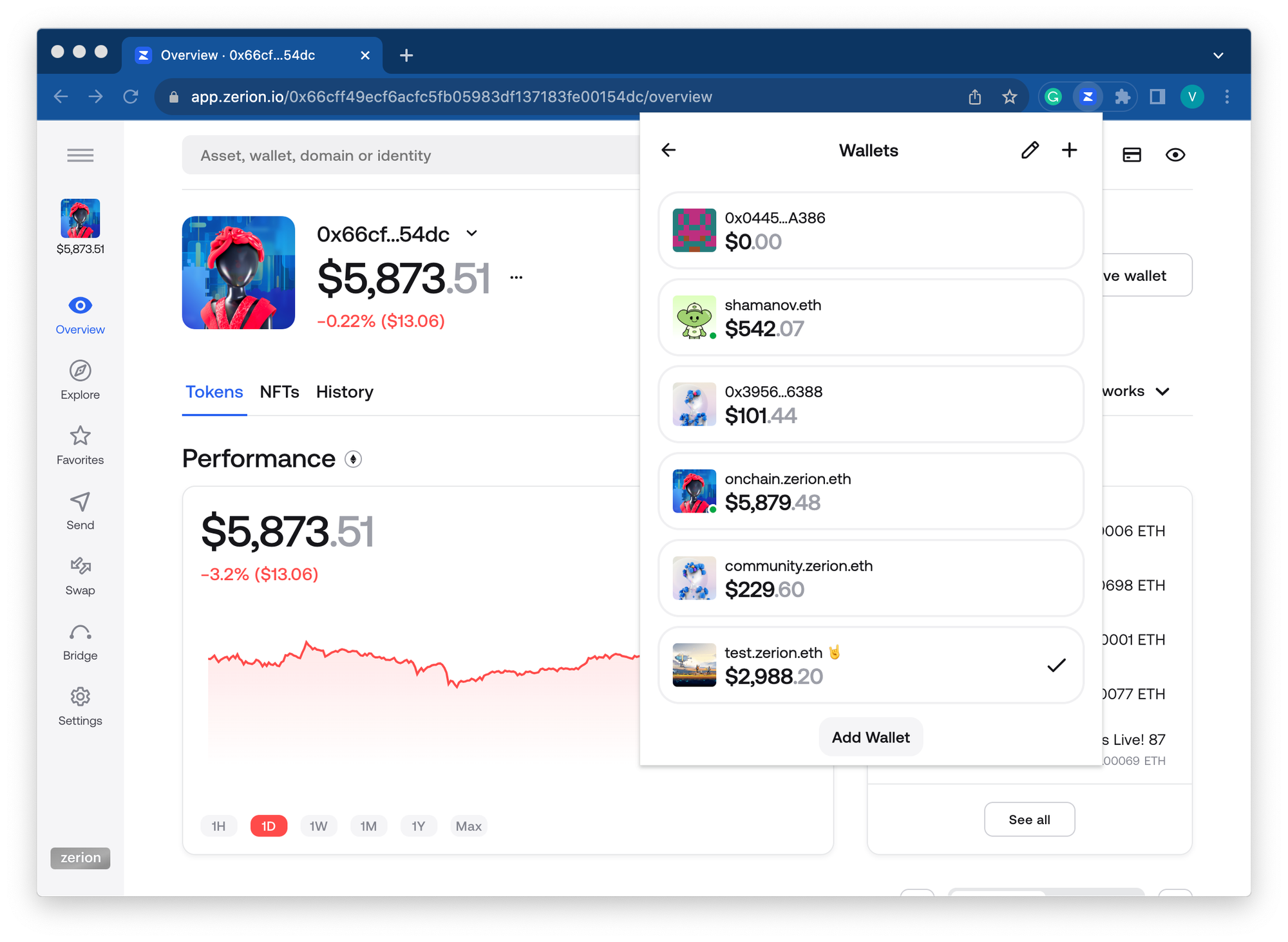
To use separate addresses, you need a wallet that makes it easy to create addresses and switch between them. Zerion Wallet makes it easy on both mobile and desktop.
4. Secure your seed phrase and private keys
Regardless of what non-custodial wallet you use, you must securely store your seed phrase.
Account abstraction, social recovery, and other ways of creating and managing non-custodial wallets might eventually remove the need for seed phrase management. For now, those projects are arguably too early to store a meaningful amount of crypto.
So you’re stuck with seed phrases for now.
How NOT to store the seed phrase
- Anywhere online in an unencrypted format (for example, in any note-taking app)
- As a file or screenshot on your phone or computer
- In a filing cabinet or other obvious physical storage places
- As a paper note in your physical wallet
In any of these places, there is a slight chance that someone can find your seed phrase. Then it’s game over.
One of the safest ways to store a seed phrase is in a fireproof safe or at least a secret stash. Besides protecting your seed phrase from criminals, consider how the seed can withstand fires, floods, or other natural disasters.
There is also a less extreme way to store your seed phrase.
iCloud / Drive backup for seed phrase
Losing a physical copy of your seed phase is an underestimated risk.
If you have ever lost your password to Google or Facebook, you know that it can be a disaster. The pain is infinitely worse if you lose your seed phrase — there is no one to restore it!
Luckily, you can store your seed phrase on iCloud or Google Drive. Of course, it should be encrypted and not stored in plain text.
Zerion mobile wallet does this for you, using Apple or Google’s built-in encryption. Your password encrypts the seedphrase. Nobody at Zerion, Apple, or Google can unencrypt it without your password (which nobody can reset for you, so make sure you safely keep it in a password manager).
Don’t get locked out of your Web3 wallet 😣
— Zerion (@zerion) September 21, 2023
1/ Introducing iCloud and Google Drive backup with Zerion pic.twitter.com/I1v4nVD1I5
Professional security auditors from Cure53 also checked this solution to minimize the risks. And, of course, this backup is entirely optional.
With this backup, if you change your phone, you can quickly restore your whole wallet from iCloud or Drive. And you don’t need to worry about ever losing your seed phrase.
Securing private keys
Your private keys are stored in your self-custodial wallet. You don’t need to write them out. And certainly, you don’t need to copy and store them anywhere online or on a hard drive.
The only time you should access your private key is to move your address to another wallet.
Do not export keys from your cold wallet. This defeats the purpose of keeping private keys in a separate, offline device.
Instead, you can connect your cold wallet to a wallet, for example, to sign crypto transactions.
Zerion mobile wallet lets you connect your Ledger via Bluetooth. This gives you the best of two worlds: the convenience of a mobile browser and the security of a cold wallet.
You can also link your Ledger to Zerion Wallet browser extension:
now you can connect your @Ledger to the zerion browser extension! pic.twitter.com/3KCBe7bvyW
— Zerion (@zerion) October 25, 2023
Finally, remember, if somebody ever asks you to share the private key in a message, that’s a scammer. This leads us to the next point.
5. Know and avoid common scams
Crypto scammers are incredibly creative. New scams come up every day.
All “mass-market” scams, aimed at small targets, try to get you to do one of three things:
- Send crypto
- Share your seed phrase or private key
- Sign a malicious transaction
To trick you into one of these actions, scammers will likely use email, social media, or other scalable channels to start the attack.
Where you can see crypto scams
You can come across crypto scams anywhere online:
- Spam email if you registered anywhere in compromised crypto services/newsletters
- Twitter DMs and replies with giveaways, airdrops, exclusive mints, etc.
- Google ads for keywords like Uniswap or Zerion, leading you to a fake page
- Spam NFTs deposited into your address
- Spam onchain transactions that make it look like an airdrop
There is a common thread across all crypto scams: they use greed and FOMO. If something looks too good, it likely is a scam.
How to avoid scams
Unfortunately, there is almost no way to avoid scams completely.
Even if you don’t use social media, email, and Google, scammers can still send you unwanted NFTs, tokens, and crypto transactions. Their aim is to get you to visit their website.
Luckily, Zerion Wallet filters out a large chunk of onchain spam — it is hidden from your portfolio and transaction history.
6. Detect phishing
The most likely crypto scam that you might encounter is a phishing website that will ask you to do one of those 3 actions: send crypto, share keys, sign a transaction.
There are two ways to protect yourself: recognize signs of crypto phishing and automatically block known phishing domains.
Common signs of phishing
Scammers usually do their best to make their phishing believable but they cannot make a fake site look 100% the real one.
Watch out for these signs:
- Wrong URL — it could be subtle, like “l” instead of “i” or some non-Latin character
- Design — there could be small inconsistencies or issues that you normally won’t see on a real website
- Wording — the voice can be off-brand or the copy can contain mistakes
If in doubt, share the link in the project’s Discord or with their support.
Luckily, many phishing domains are quickly reported, and your wallet can help you catch them.
Automatic phishing detection in Zerion Wallet
When you try to connect to a website, Zerion Wallet will automatically check the URL against Blockaid’s data.
Other crypto wallets like MetaMask also have some phishing protection.
However, Zerion Wallet is the only wallet that checks the database in real-time and by default (you don't need to enable anything). Even if the scam was reported moments before you landed on it, you’ll get the warning.
7. Understand your transactions
Ok, you are on a website that looks legit. The URL is 100% genuine. It’s even saved in your bookmarks.
But it can still be a scam…
Even the top-tier Web3 projects have been subject to attacks that manipulated their front end and requested malicious transactions. So, there is always a small risk that the website is compromised.
That’s why you need to understand what transactions you are signing.
Transaction simulation
The best way to learn more about each transaction is to simulate its outcome before you sign it.
Zerion Wallet does this with its built-in transaction simulator, which shows you what you will send and what you will get.
In some cases, the transaction simulator won’t show you useful information. That’s when it’s helpful to know what the smart contract does.
8. Understand smart contract risks
You don’t need to be a developer to use web3.
But if you have a significant amount of money in a wallet, you need to understand the risks of smart contracts:
- Bugs in code
- Backdoors that can lead to rug pulls and exit scams
- Intentionally malicious functions
All legitimate smart contracts have source code in Etherscan or its alternative (like Arbiscan for Arbitrum). Simply enter the contract address in the search field and then click on the contract. For example, here is the contract for Zerion DNA:
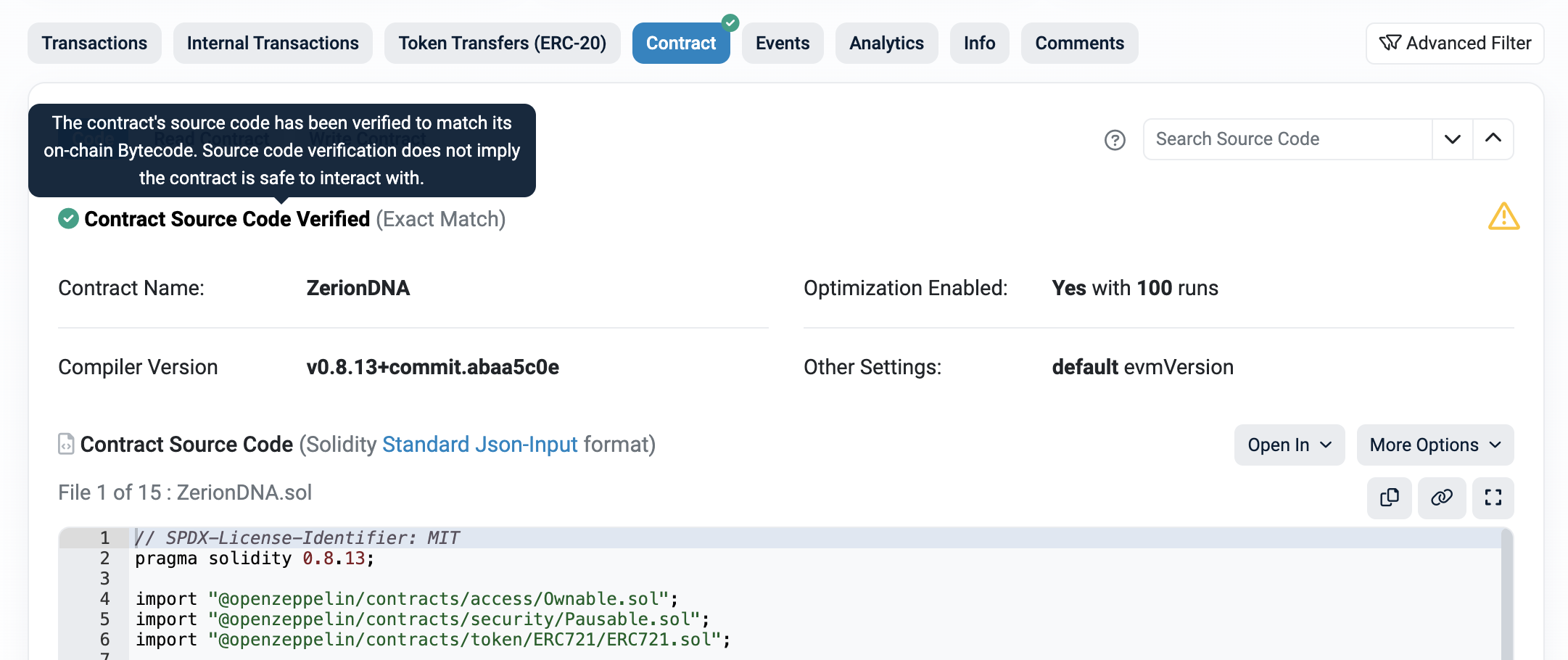
The most important part is that the contract is verified. This means the Solidity source code compiles to the same (machine-readable) bytecode that is then executed by Ethereum.
If there is no verified code on a blockchain scanner, that’s already a big red flag.
Bugs in smart contracts
Any code can contain bugs.
Even time-tested protocols can have undiscovered vulnerabilities. Unless you are a smart contract developer with free time, chances are you won’t be able to do anything here.
Instead, you should manage your portfolio to avoid putting too much money into any single protocol. For example, if you stake ETH with a staking protocol, you can spread liquidity between several protocols instead of putting it all in just one.
You can also minimize risks by not giving unlimited token allowance to any smart contract.
With Zerion Wallet, it's very easy to customize your token allowance.
1/ This is how it works: pic.twitter.com/bOb8hWyWPd
— Zerion (@zerion) September 28, 2023
Backdoors and rug pulls
Some smart contracts have built-in functions that give the project team extra control.
This can have a legitimate reason, for example, to update the dapp. But it can also lead to a rug pull when the team withdraws all liquidity and runs away with the funds. Immunefi, the bug bounty platform used by Zerion, has explored warning signs of a rug pull.
Malicious smart contracts
Finally, some smart contracts are built specifically for scams.
They will not have source code on Etherscan. If you have doubts, don’t sign the transaction. Or use your low-risk address. In Zerion Wallet, you can also easily create a new address, fund it, and use it just for that transaction.
To minimize the chance that you land on a fake website with a malicious smart contract, you can manage your existing positions from Zerion Wallet’s links.
Imagine accessing dapps for your DeFi positions, managing your @ensdomains account, reading your minted @viamirror posts — directly from your Zerion wallet?
— Zerion (@zerion) October 6, 2023
No laptop needed, zer ✌️ pic.twitter.com/OvFHUKh3Gu
9. Know where to get help if you need it
Even if you are extra careful, there could be times when things go wrong. Unfortunately, even OGs get scammed occasionally.
Before seeking help, you need to know what is possible and what is not.
What is impossible
By design, some things in Web3 are simply impossible to:
- Reverse any transaction,
- Restore a wallet without seed phrase,
- Return drained assets without the attacker’s cooperation.
If you have a problem:
What you should do
Here is how to safely get help in Web3:
- Start a chat in the wallet app — this is the safest way to avoid scammers;
- Ask the admin in Discord — there is always someone in Zerion Discord;
- Get in touch using the project's recommended support channels — for example, here is how to contact the Zerion team
The response will likely not be immediate. Please have patience and wait for a reply.
To sum up
In this post, we reviewed steps you can take to stay safe in crypto.
We started by exploring who the attackers are and who they target. We then reviewed how to choose the right wallet, manage your addresses, and secure your seed phrase and private keys. After that, we covered common scams and ways to protect against them with phishing detection and transaction simulation. We touched on the importance of understanding smart contract risks. Finally, we went over how to get help if you need it.
It’s okay if this feels overwhelming. You don’t need to drop everything and implement it. But as your onchain portfolio grows, revisit this post and take extra precautions against crypto scammers.
If you want to bring your onchain security to the next level, try Zerion Wallet.
FAQ
What is the best way to keep your cryptocurrency safe?
The best way to keep crypto safe is to store it in a self-custodial wallet. For additional security, you can keep it on a cold wallet aka hardware wallet. Avoid signing transactions with an address with lots of assets. Instead, use one address for storing high-valued assets and another for signing frequent transactions.
How can you avoid risk in cryptocurrency?
There is always some risk, like within any other asset. You can minimize some risks by storing your crypto on a self-custodial wallet and understanding what transactions you sign.
What not to do in crypto?
Never share your private keys or seed phrases. Never sign any transaction you don’t understand. Never send crypto to participate in a giveaway or an airdrop (that’s always a scam).
Can someone guess my seed phrase?
That’s extremely unlikely. Seed phrases are generated from BIP39, a list of 2049 words. So there are 2048^12 possible combinations. It is an insanely big number. This means a seed phrase is practically impossible to brute force by picking different combinations.





